#include "pam_post_auth.h"
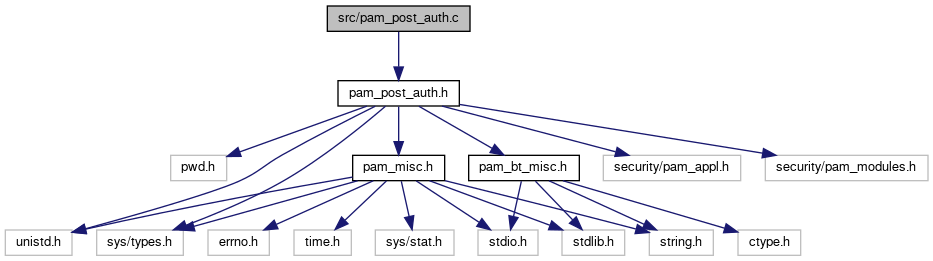
Include dependency graph for pam_post_auth.c:
Go to the source code of this file.
Functions | |
| int | exec_deauth (char *bt_addr, const char *username, FILE *log_fp, const char *trusted_dir_path) |
Function Documentation
◆ exec_deauth()
| int exec_deauth | ( | char * | bt_addr, |
| const char * | username, | ||
| FILE * | log_fp, | ||
| const char * | trusted_dir_path | ||
| ) |
Once Authenticated, run the deauth background service
NOTE: exec replaces the child process. Memory mappings are not preservered on an exec() call so memory is reclaimed apparently. NOTE: will set the euid to be the user instead of root
- Parameters
-
bt_addr the trusted bluetooth address we want to log in username the user we want to run the program as (i.e. should be the username of the user who wishes to login)
Definition at line 3 of file pam_post_auth.c.
Here is the call graph for this function:
